Trump's NSC used insecure Gmail accounts for official business
DPRK IT workers are targeting Europe after US indictments and sanctions, UK cyber bill details revealed, Firing HHS workers might weaken medical device security, Chinese military-linked VPN apps found on play stores, Gmail E2EE rolling out, Robot dog has serious flaw, much more


Metacurity is a reader-supported publication that requires a lot of work and relies on the generous support of our paid readers. Please consider supporting Metacurity with an upgraded subscription. Thank you.
If you can't commit to a subscription today, please consider donating whatever you can. Thank you!
To the dismay of cybersecurity professionals and in the latest example of questionable data security practices by Donald Trump's top national security officials, members of his National Security Council (NSC), including White House national security adviser Michael Waltz, have conducted government business over their insecure personal Gmail accounts.
According to emails reviewed by The Post, a senior Waltz aide used the commercial email service for highly technical conversations with colleagues at other government agencies about sensitive military positions and powerful weapons systems related to an ongoing conflict. While the NSC official used his Gmail account, his interagency colleagues used government-issued accounts, headers from the email correspondence show.
Officials said Waltz has had less sensitive but potentially exploitable information, such as his schedule and other work documents, sent to his Gmail. Like others, the officials spoke on the condition of anonymity to describe what they viewed as problematic handling of information. The officials said Waltz would sometimes copy and paste from his schedule into Signal to coordinate meetings and discussions.
This revelation follows news that Waltz has also created and hosted other Signal chats with Cabinet members on sensitive topics, including Somalia and Russia’s war in Ukraine.
Trump has strongly backed Waltz, but on Wednesday, he met with Vice President JD Vance, Chief of Staff Susie Wiles, and others to discuss whether to keep him on. A day later, he informed aides he was not firing Waltz. Still, it was mainly out of a desire to avoid giving the “liberal media a scalp,” said a senior administration official. (John Hudson / Washington Post, Alexander Ward, Josh Dawsey and
Meridith McGraw / Wall Street Journal and Maggie Haberman and Tyler Pager / New York Times)
Related: Gizmodo, The Dispatch, Defense One, Nextgov/FCW, Daily Kos, Daily Mail, The Bulwark, Euromaidan Press, New Republic, r/cybersecurity, r/politics, Raw Story, The Verge, Engadget, The Gateway Pundit, The Independent, San Francisco Chronicle, The Register, Axios, Mediaite, American Oversight, HuffPost, Bloomberg, Defense One, Euromaidan Press, Daily Kos, Nextgov/FCW, The Bulwark, Foreign Policy, The Guardian, Raw Story
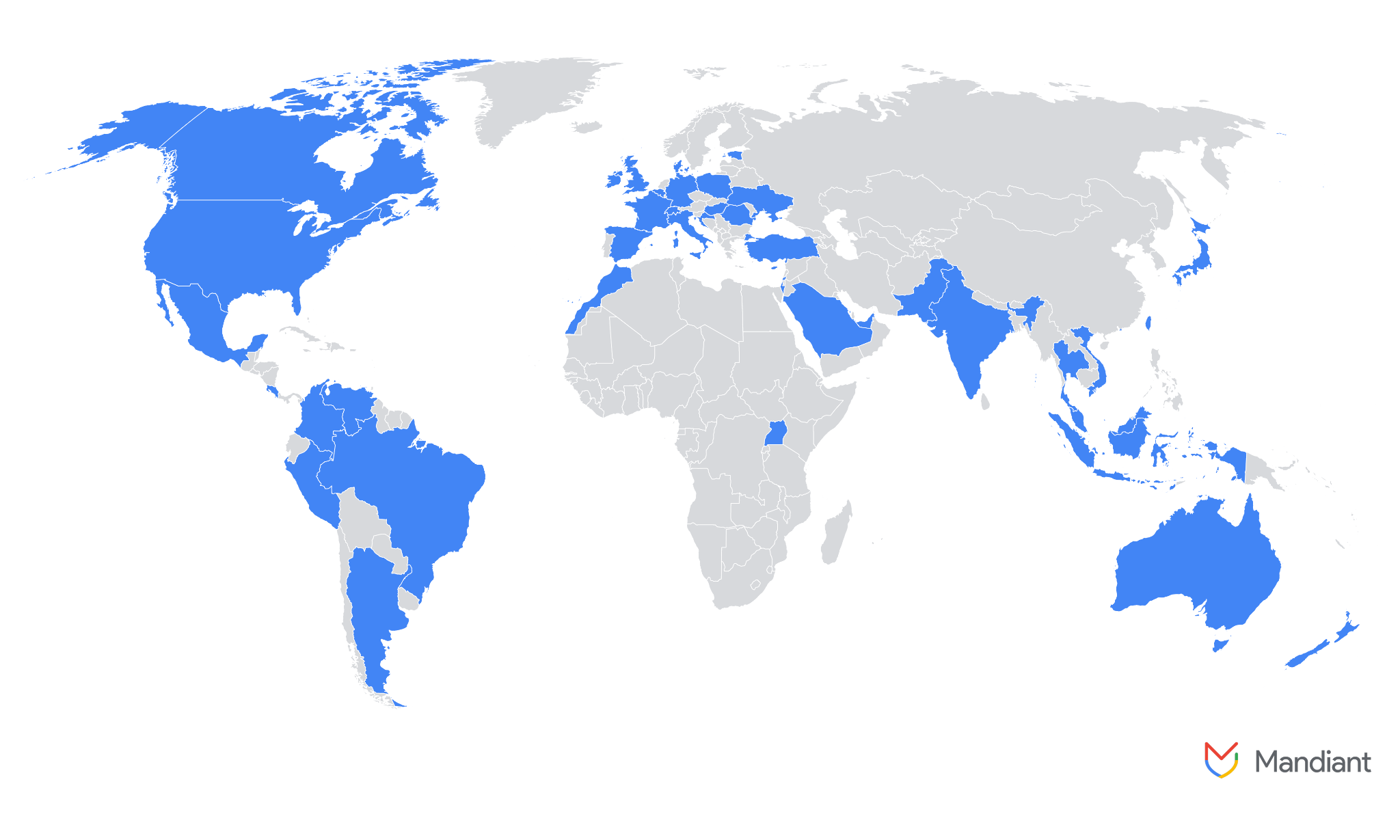
Researchers with Google Threat Intelligence Group (GTIG) report that North Korea's IT workers have expanded operations beyond the United States and are increasingly targeting organizations across Europe.
They say North Korea's IT army has increasingly targeted positions at companies in Germany, Portugal, and the United Kingdom after many of its members have been charged and targeted with sanctions in the United States.
"In their efforts to secure these positions, DPRK IT workers employed deceptive tactics, falsely claiming nationalities from a diverse set of countries, including Italy, Japan, Malaysia, Singapore, Ukraine, the United States, and Vietnam. The identities used were a combination of real and fabricated personas," said Jamie Collier, a lead threat intelligence advisor at GTIG.
"IT workers in Europe were recruited through various online platforms, including Upwork, Telegram, and Freelancer. Payment for their services was facilitated through cryptocurrency, the TransferWise service, and Payoneer, highlighting the use of methods that obfuscate the origin and destination of funds."
GTIG's report follows multiple warnings issued by the FBI regarding North Korea's massive army of IT workers sent abroad to generate revenue, who have tricked hundreds of companies in the United States and worldwide into hiring them over the years. It also follows indictments by the US Justice Department against undercover North Korean IT workers and the US Treasury's Office of Foreign Assets Control (OFAC) sanctioning of North Korean front companies linked to North Korea's Ministry of National Defense. (Sergiu Gatlan / Bleeping Computer)
Related: Google Cloud, IT Pro, Help Net Security, The Register, Cointelegraph, Security Brief Australia, Decrypt, CoinDesk, Decrypt, crypto.news, Blockonomi, Help Net Security, Bloomberg Law, NK News, PCMag, CSO, r/cybersecurityr, r/europe
The UK's technology secretary, Peter Kyle, revealed the full breadth of the government's Cyber Security and Resilience (CSR) Bill for the first time this morning, pledging £100,000 ($129,000) daily fines for failing to act against specific threats under consideration.
The CSR bill, slated to enter Parliament later this year, was teased in the King's Speech in July, shortly after the Labour administration came into power. The gist communicated at the time was to strengthen the NIS 2018 regulations and future-proof the country's most critical services from cyber threats.
Kyle said the CSR bill comprises three key pillars: expanding the regulations to include more types of organizations, giving regulators greater enforcement powers, and ensuring the government can change the regulations quickly to adapt to evolving threats.
Additional amendments are under consideration and may add to the confirmed pillars by the time the legislation passes official procedures. These include bringing data centers into scope, publishing a unified set of strategic objectives for all regulators, and giving the government the power to issue ad hoc directives to in-scope organizations. (Connor Jones / The Register)
Related: GOV.uk, NCSC, Industrial Cyber, Infosecurity Magazine, Cyber Magazine, IT Pro, CSO Online, Bank Info Security, Computing, SC Media, Open Access Government
During a hearing of a House Committee on Energy and Commerce subcommittee, multiple members peppered five medical device cybersecurity experts with questions about how the firings of at least 10,000 workers from the Department of Health and Human Services will impact efforts to check the devices for cybersecurity protections before and after they are sold to hospitals.
“I have difficulty seeing how we have a hearing about how the FDA should approach legacy medical device cybersecurity without first addressing the fact that the Trump administration and DOGE are dismantling the very agency responsible for medical device safety,” said Rep. Yvette Clarke (D-NY).
Clarke noted that in February, the Trump administration fired hundreds of people from the FDA's Center for Devices and Radiological Health (CDRH) but has declined to say how many are involved in medical device cybersecurity.
She said that HHS has told Democratic lawmakers that the latest round of firings would not impact medical device reviewers but would not address the many other HHS employees who are not technically reviewers and hold significant roles related to the cybersecurity verification process.
A 2022 bill mandated that medical device manufacturers abide by new cybersecurity rules and submit devices for verification by the FDA.
Representative Alexandria Ocasio-Cortez (D-NY) noted during her questions that medical device firms, hospitals, and the federal government have all called for more cybersecurity-focused employees at the FDA to help move along devices they wanted to release.
She focused her ire on Tesla CEO Elon Musk, who has taken on an outsized role in the federal government as head of the Department of Government Efficiency (DOGE).
In February, Musk fired over 700 FDA employees, including about 200 specifically from the CDRH. But Musk quickly scrambled to rehire some of the employees and specifically brought back the medical reviewers of Neuralink, a neurotechnology company he founded, Ocasio-Cortez said. (Jonathan Greig / The Record)
Related: Energy and Commerce Committee, American Hospital Association, MedPage Today, Cyberscoop
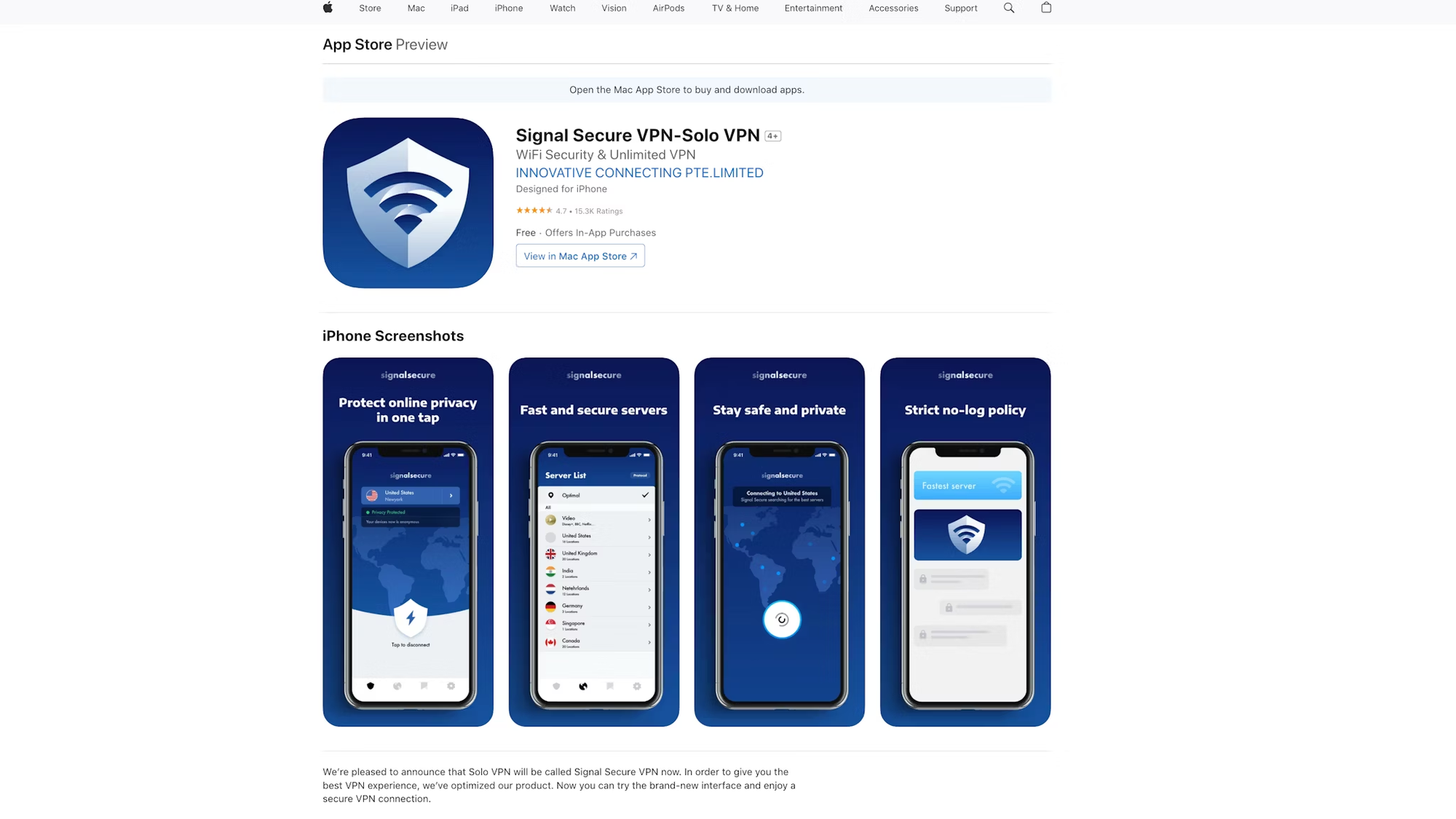
A joint investigation by the Tech Transparency Project and the Financial Times found that at least five VPN apps in Apple's App Store and Google Play Store had links to the Chinese military, with three racking up millions of downloads.
The five apps include Turbo VPN, VPN Proxy Master, Thunder VPN, Snap VPN,
and Signal Secure VPN (not associated with the Signal messaging app)
After the Financial Times alerted Apple, the company removed Thunder VPN and Snap VPN from the App Store. The fate of the three remaining apps is unclear. (Ben Lovejoy / 9to5Mac)
Related: Financial Times, Tech Transparency Project, AppleInsider, Cryptopolitan, TipRanks Financial, Telecoms Tech News
Sponsored Item
Authentication and deepfakes are the next big challenge
(Las Vegas, NV) In early 2024, a finance worker at an unnamed multinational corporation was deceived by a deepfake video of the company’s CFO into paying a scammer $25 million, setting a publicly known high watermark in the emerging era of AI-generated identity crimes.
It’s no surprise, then, that increasingly realistic deepfakes, stolen identities, and authentication scams were among the key themes at Slovakian cybersecurity company ESET’s annual global cybersecurity conference here. CEO Richard Marko told attendees during an opening talk that ESET itself has been subjected to AI fakery that seeks to exploit the privately held company’s reputation, rapid growth, and longevity in the cybersecurity world.
“We have our own experience here because ESET is one of the major central security vendors,” Marko said. “News spread that ESET might be going public, being practically the last really big privately owned vendor still owned by its original founders and engineers. It naturally attracts attention and looks like a good investment opportunity.”
Consequently, “almost every week we see a new video of either me or some of the founders talking about how beautiful this and is and how good it will be to invest there,” Marko said.
Verifying the identity of people and organizations in the digital realm will be the next significant challenge for cybersecurity, ESET’s CTO, Juraj Malcho, told Metacurity. “There was this crazy case of the $25 million lost,” he said. “These things can happen. If someone is going after you, they will make that effort because it is a lot of money. We all need to be aware.”
It would be helpful if users could become more discerning about the information they receive, Malcho said. “Think about the information you are receiving. Is it something that you intentionally want to obtain? If not, ignore it, whether it is a Nigerian scam or a great video. We need to consider the real value of information and if it is relevant to you.”
In the long run, however, new methods will need to be devised to authenticate the identity of information senders. “We will eventually need methods to verify ‘Oh, is that really you,’” Malcho said. “We will need to confirm that this is the entity and sign it.”
From an organizational perspective, dealing with these kinds of next-generation problems or coping with advanced adversaries, such as nation-states, is not a technical problem, ESET senior malware researcher Robert Liposky told Metacurity. The solutions are well understood. It’s just a question of implementing them.
“There are valid reasons why things are not ideal, but it's not like we are struggling to find the solution,” Liposky said. “We know what the solutions are; we know what the recommendations are. If we lived in an ideal world, which we don't, of course, but if those recommendations were followed, the adversaries would have a much harder time."
As always, the most effective solution is for organizations to dedicate the necessary effort to establishing robust security programs. “Really evaluate where you fit in, what your risk status is, what your resilience status is, and whether this responsibility of securing the environment should be handled internally or offloaded to external firms,” Liposky said. “That would be my general recommendation.”
Note: Although this is a sponsored news item, Metacurity made all editorial choices, including the topic, and the sponsor did not review the content in advance.
Google has started rolling out a new end-to-end encryption (E2EE) model for Gmail enterprise users, making sending encrypted emails to any recipient easier.
While businesses also have the option to configure the Secure/Multipurpose Internet Mail Extensions (S/MIME) protocol to send digitally signed and encrypted messages, this requires significant resources, including deploying certificates to all users and exchanging them before sending the emails.
Google says that after Gmail's new E2EE model rolls out, business users will be able to send fully encrypted emails to any user on any email service or platform without having to worry about complex certificate requirements.
To send a new encrypted email, Gmail users only have to turn on the "Additional encryption" option when writing the message. The email will be automatically decrypted when the recipient is a Gmail user with an enterprise or personal account.
Recipients using Google's Gmail mobile app or non-Gmail email clients will receive a link to sign in and view the email in a restricted version of Gmail. The recipient can then use a guest Google Workspace account to view and reply to the encrypted message. (Sergiu Gatlan / Bleeping Computer)
Related: Google, ZDNet, CSO Online, The Register, Dark Reading, Forbes, Infosecurity Magazine, Silicon Angle, Cybernews, PCMag, Techzine, Security Week, GBHackers, SC Media, Axios, Computer Weekly
A recent discovery by security researchers at Berlin-based startup thinkAwesome GmbH has revealed a significant security flaw in the popular Unitree Go1 robot dogs that allowed anyone with the default credentials and a specific API key to control the robots and access their cameras.
The researchers identified 1,919 vulnerable devices, some located outside China, including in academic and corporate networks worldwide. While the researchers did not find evidence of intentional backdoor implantation, they attribute the vulnerability to inadequate code review practices at Unitree Robotics.
The security flaw poses serious risks, particularly in sensitive environments where unauthorized parties could remotely access and control robot dogs.
The researchers urge users of the Unitree Go1 to remove the devices from their networks and examine their systems for potential breaches. The risk remains that similar vulnerabilities could exist in newer versions of the robot or other products from the manufacturer. (iHLS)
Related: Think-Awesome, Security Week, Cybernews
Russia’s state-owned railway, RZD, reported being the target of a DDoS attack that temporarily disrupted its website and mobile application.
It’s the second incident this week involving a Russian transportation agency, following disruptions with the app and website for Moscow’s subway system on Monday.
RZD confirmed that its online services were unavailable due to a distributed denial-of-service (DDoS) attack. However, ticket sales remained operational at physical offices across stations and terminals.
“We are working to restore their operation as quickly as possible,” RZD said, without providing any details about the scale of the attack or when it will be able to restore its services. (Daryna Antoniuk / The Record)
Related: Anadolu Ajansı, The Moscow Times, Ukrainska Pravda
Attackers are now targeting a critical authentication bypass vulnerability in the CrushFTP file transfer software using exploits based on publicly available proof-of-concept code.
Outpost24 reported the security vulnerability (CVE-2025-2825), which allows remote attackers to gain unauthenticated access to devices running unpatched CrushFTP v10 or v11 software.
"Please take immediate action to patch ASAP. The bottom line of this vulnerability is that an exposed HTTP(S) port could lead to unauthenticated access," CrushFTP warned in an email sent to customers on Friday, March 21, when it released patches to address the security flaw.
As a workaround, admins who can't immediately update CrushFTP 10.8.4 and later or 11.3.1 and later can enable the DMZ (demilitarized zone) perimeter network option to protect their CrushFTP servers until they can patch.
A week later, security threat monitoring platform Shadowserver warned that its honeypots detected dozens of exploitation attempts targeting Internet-exposed CrushFTP servers, with over 1,500 vulnerable instances exposed online.
The warning comes days after ProjectDiscovery published a write-up containing CVE-2025-2825 technical details and a proof-of-concept exploit.
"We are observing CrushFTP CVE-2025-2825 exploitation attempts based on publicly available PoC exploit code," Shadowserver said on Monday. "Still 1512 unpatched instances vulnerable to CVE-2025-2825 seen on 2025-03-30." (Sergiu Gatlan / Bleeping Computer)
Related: CrushFTP, Attackerkb, Project Discovery, SC Media, Security Week, Help Net Security, Heise Online
Blockchain security firm Cyvers reported that an unauthorized party withdrew about $70 million in digital assets from the open-source payment platform UPCX.
The firm said it found suspicious activity involving 18.4 million UPC tokens and estimated the value of the compromised funds at $70 million.
Cyvers said someone accessed a UPCX address and upgraded its ProxyAdmin contract. The attacker then executed a function that allows admins to withdraw, leading to fund transfers from three different management accounts.
As of yesterday, the stolen tokens had not been swapped for other crypto assets. (Ezra Reguerra / Cointelegraph)
Related: Cybernews, Tron Weekly, Cryptoslate, CoinmarketCap, BeInCrypto
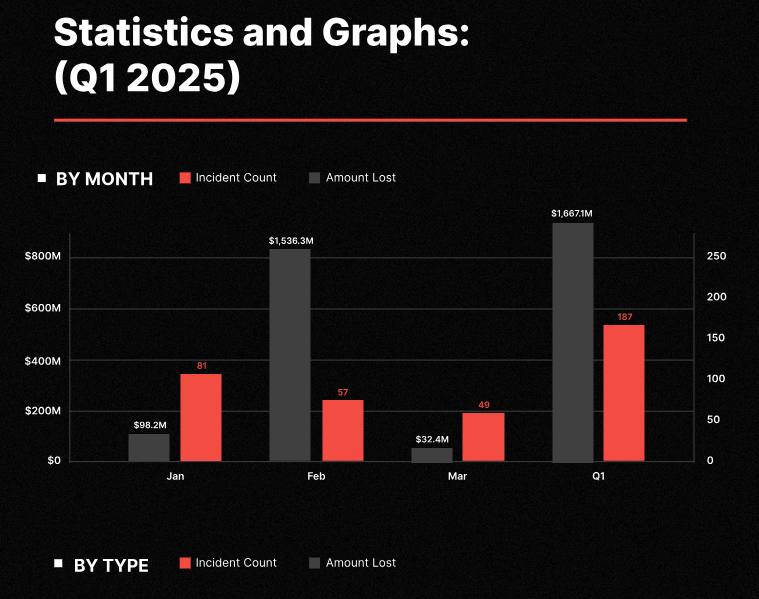
Blockchain security firm CertiK reports that losses to crypto scams, exploits, and hacks dropped to just $28.8 million in March, far from February’s spike to $1.5 billion in losses after the Bybit hack.
Code vulnerabilities accounted for the most losses, at over $14 million, while wallet compromises were used to steal over $8 million.
The most significant loss for the month was the $13 million March 25 smart contract exploit of the decentralized lending protocol Abracadabra.money. (Stephen Katte / Cointelegraph)
Related: Certik, Korea IT Times
Microsoft says it used its AI-powered Security Copilot to discover 20 previously unknown vulnerabilities in the GRUB2, U-Boot, and Barebox open-source bootloaders.
GRUB2 (GRand Unified Bootloader) is the default boot loader for most Linux distributions, including Ubuntu, while U-Boot and Barebox are commonly used in embedded and IoT devices.
Microsoft discovered eleven vulnerabilities in GRUB2, including integer and buffer overflows in filesystem parsers, command flaws, and a side-channel in cryptographic comparison.
Additionally, nine buffer overflows in parsing SquashFS, EXT4, CramFS, JFFS2, and symlinks were discovered in U-Boot and Barebox, which require physical access to exploit.
The newly discovered flaws impact devices relying on UEFI Secure Boot. If the right conditions are met, attackers can bypass security protections to execute arbitrary code on the device.
While exploiting these flaws would likely need local access to devices, previous bootkit attacks like BlackLotus achieved this through malware infections.
Microsoft says Security Copilot dramatically accelerated the vulnerability discovery process in a large and complex codebase, such as GRUB2, saving approximately 1 week that would be required for manual analysis. (Bill Toulas / Bleeping Computer)
Related: Microsoft Security Blog, GBHackers Security, Cyber Security News, Security Week
Microsoft’s Offensive Research and Security Engineering (MORSE) team discovered that drivers associated with several Canon production printers, office multifunction printers, and laser printers are affected by an out-of-bounds vulnerability now tracked as CVE-2025-1268 with a CVSS severity score of 9.4.
Canon told users that exploiting the vulnerability can allow an attacker to prevent printing or potentially execute arbitrary code “when the print is processed by a malicious application."
Users have been advised to check Canon websites for patched versions of the vulnerable printer drivers. (Eduard Kovacs / Security Week)
Related: Canon, The Cyber Express, GBHackers, Heise Online, Security Affairs
Best Thing of the Day: How the Cybersecurity Skills Shortage Evaporated
For the second day in a row, Dragos' Lesley Carhart has produced a helpful guide, this time one that clarifies what happened to the cybersecurity skills shortage and how the employment market for cybersecurity workers got so muddled.
Bonus Best Thing of the Day: Greece Wants to Hire Cyber Workers
Cyber workers seeking jobs may want to look at Greece, where the National Intelligence Service (EYP) kicked off its first significant recruitment drive in five years, targeting 310 new cyber-related hires by the end of 2025.
Worst Thing of the Day: Your Paywalls Mean Nothing to Us
A new paper by the AI Disclosures Project accuses OpenAI of increasingly relying on non-public books, which it didn’t license to train more sophisticated AI models.
Closing Thought