Trump fired NSA head Haugh at right-wing conspiracist Loomer's instigation
Hackers stole half a million from Australia's superannuation funds, Russian hacker sentenced to two-years in a penal colony for DDoS attack on local company, Texas State Bar hit by INC ransomware gang, Threat actors ramping up US tax day scams, Hard-to-remove Android spyware app emerges, much more


Check out my latest news item for CSO on the firing of NSA and Cybercom Director Timothy Haugh.
Metacurity is a reader-supported publication that requires a lot of work and relies on the generous support of our paid readers. Please consider supporting Metacurity with an upgraded subscription. Thank you.
If you can't commit to a subscription today, please consider donating whatever you can. Thank you!
At the instigation of right-wing conspiracy theorist and anti-immigrant advocate Laura Loomer, Donald Trump fired Gen. Timothy D. Haugh, who led both the National Security Agency and US Cyber Command, along with his civilian deputy Wendy Noble.
Haugh, who reportedly had been traveling, and Noble were apparently given no reason for their termination. However, Loomer appeared to take credit for the firing, writing in a post on X after midnight that General Haugh “had no place” serving in the administration because he had been chosen for the job by Gen. Mark A. Milley, the former chairman of the Joint Chiefs who has been critical of Mr. Trump.
“Why would we want an NSA Director who was referred to Biden after being hand selected by Milley,” Ms. Loomer wrote. “Why would we want Milley’s hand picked choice for NSA DIRECTOR? We do not! And he was referred for firing.”
One official said former official said Lt. Gen. William J. Hartman, the deputy at Cyber Command, would serve as the acting director of the NSA.
Loomer was also ostensibly involved in firing at least five key aides on the National Security Council, whom Loomer deemed disloyal. Trump called Loomer “a great patriot” who makes recommendations on people, and “sometimes I listen to those recommendations,” but he denied that she was involved in the NSC dismissals.
Democratic lawmakers excoriated the firing of Haugh and Noble. Senator Mark Warner said, “At a time when the United States is facing unprecedented cyberthreats, as the Salt Typhoon cyberattack from China has so clearly underscored, how does firing him make Americans any safer?” (Julian E. Barnes / New York Times, Ellen Nakashima, John Hudson and Michael Birnbaum / Washington Post and Ellen Nakashima, Warren P. Strobel and Aaron Schaffer / Washington Post)
Related: Wall Street Journal, NBC News, Washington Post, Financial Times, UPI, CNN, The Record, Axios, Bloomberg, CBS News, USA Today, Reuters, Associated Press, Axios, BBC News, CNN, Reuters, The Record, r/technology, TechCrunch, CSO Online
The Association of Superannuation Funds of Australia (ASFA) says hackers targeted Australian superannuation funds, or retirement funds, this week, with a small number of customers losing a combined half a million dollars and hackers compromising some members’ data.
ASFA said hackers attempted to breach the cyber defenses of several superannuation funds last weekend. While most attempts were stopped, several companies were affected.
“Retirement savers should be assured superannuation funds and their service providers already have rigorous cyber protections in place,” ASFA said in a statement.
National cyber security co-ordinator Lieutenant General Michelle McGuinness confirmed that Hostplus, Rest, AustralianSuper, and Australian Retirement Trust were among the funds affected by the attack. McGuinness said superannuation and banking firms were working with government agencies to respond to the attack.
Insignia Financial, which oversees brands including MLC and IOOF, said about 100 accounts on its Expand platform had been targeted, but no financial impact to customers had been detected.
Rest said 8000 accounts may have accessed personal information, but no funds were transferred.
AustralianSuper, which has more than 3.4 million members, confirmed that four of its members had a collective $500,000 taken from their accounts. Stolen passwords were used to log into the accounts of 600 members and attempt fraud.
The fund advised members to log into their accounts to ensure their bank and contact details were correct and that their account password was strong and unique. (Josh Taylor / The Guardian)
Related: Reuters, ABC.net.au, News.com, Financial Review, The Conversation, Pedestrian TV, Colitico, Cyber Daily, Financial Newswire, Daily Mail, 9News, 7News, TheNightly, LiSTNR, SBC News, Professional Planner, Bloomberg
A Russian citizen from the Rostov region was sentenced to two years in a penal colony for launching a distributed denial-of-service (DDoS) attack against a local tech company.
According to the Federal Security Service (FSB), he was convicted of organizing a paid DDoS attack in April 2024 against a company classified as part of Russia’s critical information infrastructure. In addition to the prison sentence, he was fined 500,000 rubles (approximately $5,400).
The Russian agency didn’t specify who paid the suspect for the attack, but in previous cases, it has blamed Ukrainian intelligence agencies for recruiting Russian citizens to carry out sabotage, espionage, and cyber campaigns inside the country.
Russian security agencies have increasingly reported cases involving local hackers allegedly working against the state or cooperating with foreign entities. (Daryna Antoniuk / The Record)
Related: Interfax
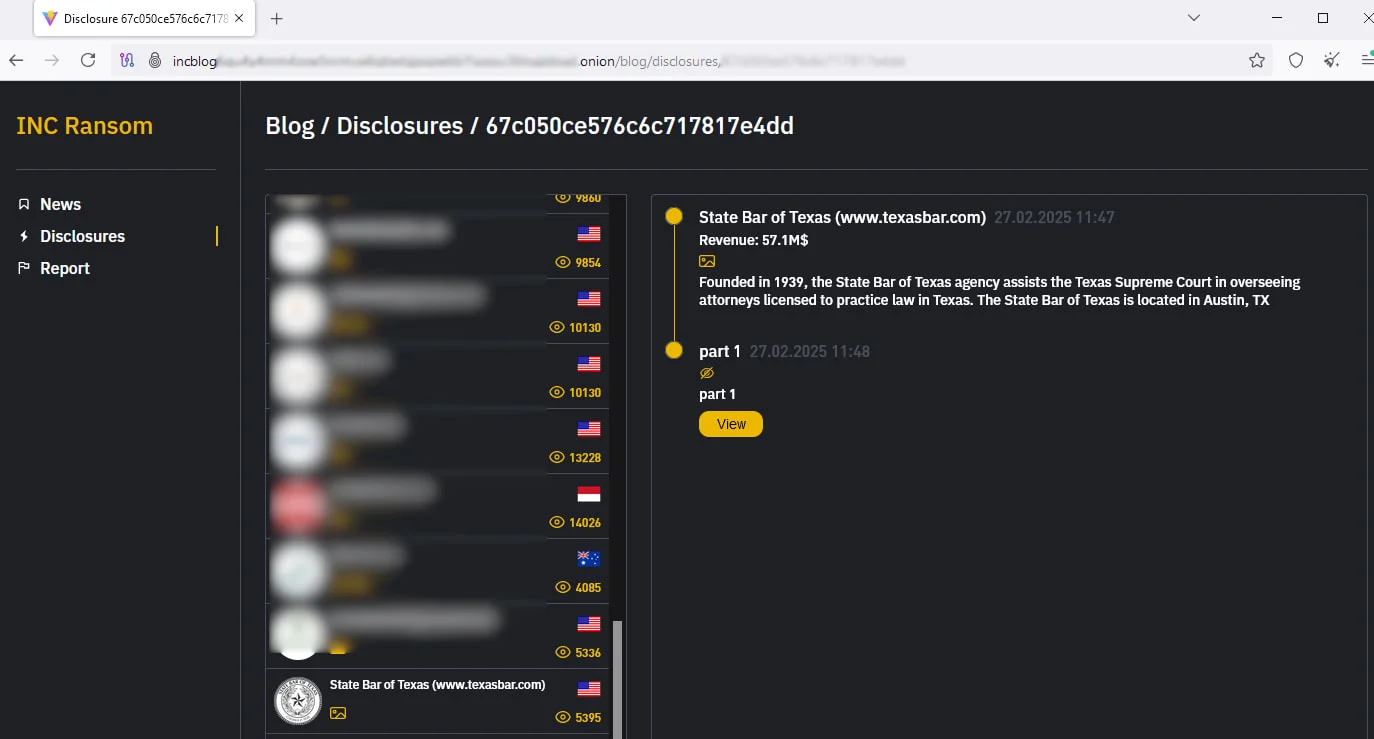
The State Bar of Texas, the second-largest bar association in the US, is warning that it suffered a data breach after the INC ransomware gang claimed to have breached the organization and began leaking samples of stolen data.
In a notification letter sent to affected members, the organization states that it suffered a security breach between January 28 and February 9, 2025, but it was only discovered on February 12.
The threat actors were able to steal information from the network, including full names and other data that is redacted in the public data breach notifications filed with Attorney Generals' offices.
"Through the investigation, we determined that there was unauthorized access to our network between January 28, 2025, and February 9, 2025," reads the notice.
"During this time, the unauthorized actor was able to take certain information from our network."
The INC ransomware gang claimed an attack against the State Bar of Texas by adding the organization to its dark web extortion page on March 9, 2025. The threat actors have already leaked samples of allegedly stolen files, including legal case documents. (Bill Toulas / Bleeping Computer)
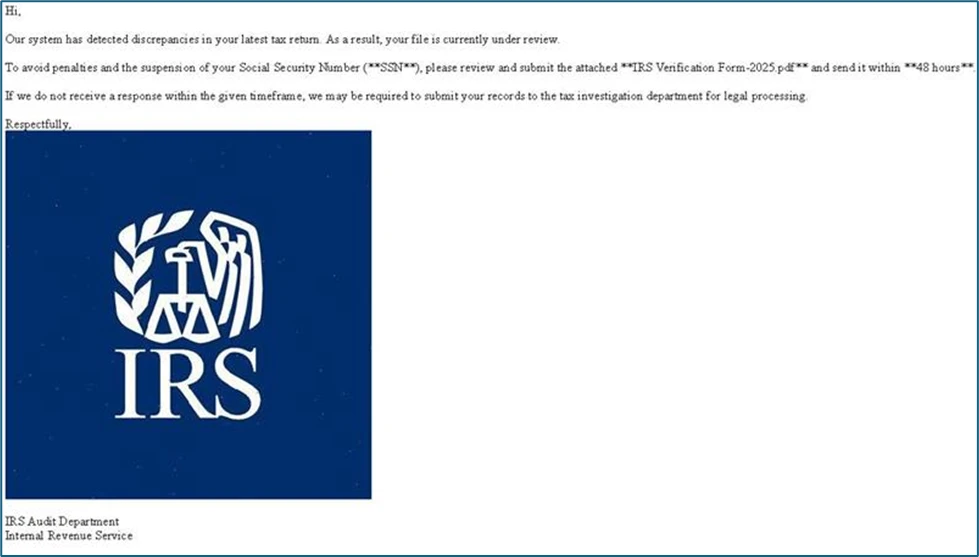
Microsoft Threat Intelligence is warning of several phishing campaigns taking advantage of the approaching Tax Day in the US on April 15th.
“Threat actors craft campaigns that mislead taxpayers into revealing sensitive information, making payments to fake services, or installing malicious payloads,” Microsoft said.
“Although these are well-known, longstanding techniques, they could still be highly effective if users and organizations don’t use advanced anti-phishing solutions and conduct user awareness and training.”
At least four threat actor groups deliver thousands of phishing emails and other lures. Thousands of tax-themed phishing emails, often masquerading as coming from the IRS, landed in inboxes in an attempt to deliver malware. This campaign is attributed to a threat actor labeled Storm-0249, an access broker active since 2021 and known for distributing various malicious packages.
RaccoonO365 also targets businesses with a phishing-as-a-service provider that offers cybercriminals a suite of tools, including phishing kits that mimic Microsoft 365 sign-in pages. Hackers also mimic the IRS by sending Americans phishing emails, luring victims to verify their “potential eligibility for a tax refund.”
Finally, phishers pretend to be fake personas, asking for tax filing services and prices and building rapport by exchanging messages. If the recipient replies, scammers send them their fake “income documents.” (Ernestas Naprys / Cybernews)
Related: Microsoft
A stealthy phone monitoring app for Android that requires a password to uninstall is effectively blocking Android device owners from being able to remove the app.
The app relies on whoever is planting the app to enable a built-in feature in Android that allows apps to “overlay” content on top of all other apps. Once granted this permission, the spyware app uses this overlay access to forcibly display a password prompt whenever the user tries to uninstall or deactivate the app through Android’s settings.
Moreover, the password to uninstall this spyware is set by whoever planted it.
TechCrunch’s testing found that rebooting an affected Android device into “safe mode” temporarily prevents third-party apps from loading, including the spyware, allowing affected individuals to remove the app without the password prompt appearing. (Zack Whittaker / TechCrunch)
Related: GBHackers
Google ramped up the release of its AI reasoning model, Gemini 2.5 Pro, to late March but has yet to publish safety reports for its latest models, including Gemini 2.5 Pro and Gemini 2.0 Flash, raising concerns that the company is prioritizing speed over transparency.
It’s relatively standard for frontier AI labs—including OpenAI, Anthropic, and Meta—to report safety testing, performance evaluations, and use cases whenever they launch a new model.
These reports, sometimes called “system cards” or “model cards,” were proposed years ago by researchers in industry and academia. Google was among the first to suggest model cards in a 2019 research paper, calling them “an approach for responsible, transparent, and accountable practices in machine learning.”
Google’s director and head of product for Gemini, Tulsee Doshi, said that the company hasn’t published a model card for Gemini 2.5 Pro because it considers the model an “experimental” release. The goal of these experimental releases is to put an AI model out in a limited way, get feedback, and iterate on the model ahead of a production launch, she said.
According to Doshi, Google intends to publish Gemini 2.5 Pro’s model card when it makes the model generally available. The company has already done safety testing and adversarial red teaming. (Maxwell Zeff / TechCrunch)
Related: Fast Company
Best Thing of the Day: We Need All the Help We Can Get Probing Digital Crime
US Senators Catherine Cortez Masto (D-NV) and Chuck Grassley (R-IA) introduced legislation that would relax rules that limit the Secret Service's jurisdiction over unlicensed money-transmitting businesses, allowing it to investigate all new forms of criminal activity involving digital assets.
Bonus Best Thing of the Day: Fighting Fire with Fire
AI research organization Palisade Research has built a system called LLM Agent Honeypot to detect AI agents that have been developed to conduct cyberattacks.
Worst Thing of the Day: Missing G-D Logs
According to Sophos' 2025 Active Adversary Report, in 2024, logs were missing in 47% of cases handled by the Sophos team, with 66% missing for incident response.
Closing Thought