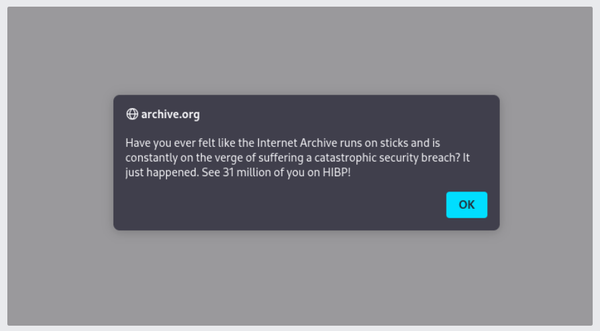
Miserable Miscreants Targeted Internet Archive's Wayback Machine, Stole 31 Million Records
China's SweetSpecter sent phishing emails to ChatGPT staff, FTC requires Marriott and Starwood to bolster cybersecurity, India's Star Health and Allied Insurance confirm cyberattack, Crypto kid thief's parents subject to botched kidnapping, Bitfinex was sole victim of RazzleKhan couple, much more











