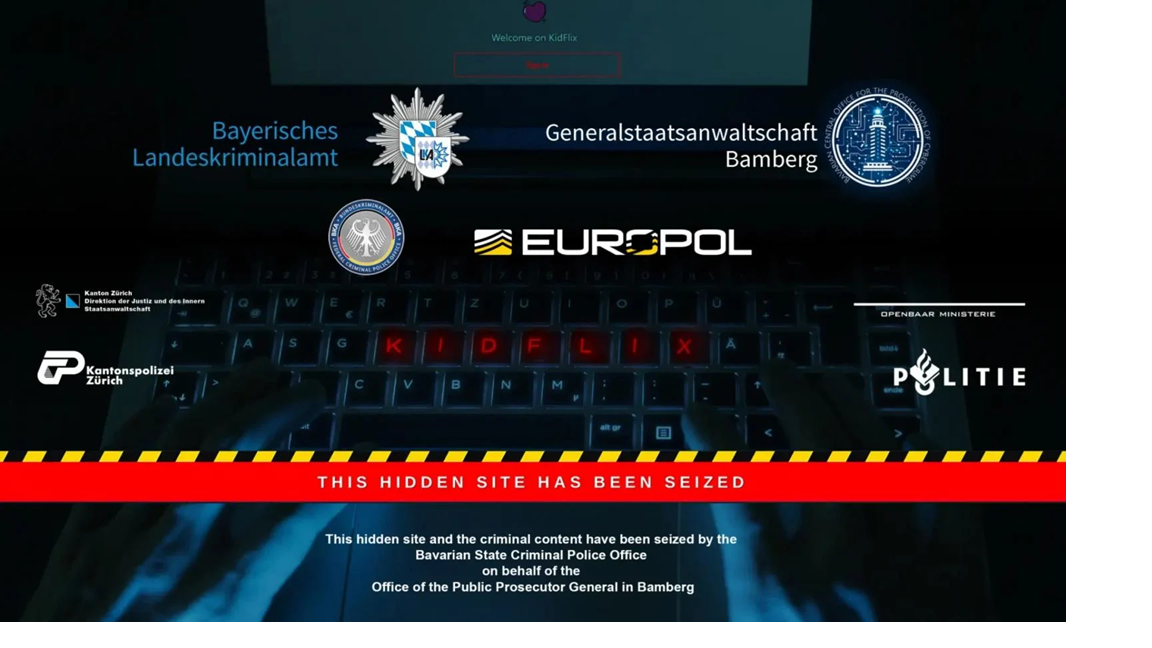
Joint law enforcement operation took down the dark web CSAM platform Kidflix
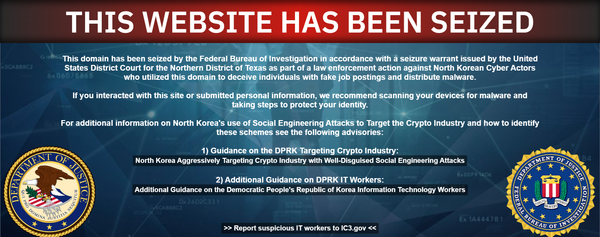
Waltz had at least 20 Signal group chats going, Indiana cyber prof has not been detained or charged, Musk worker bragged about hacking and pirating software, Oracle had a second breach, NSA and others warn of C2 creator Fast Flux, Royal Mail and Samsung Germany breached via same supplier, much more