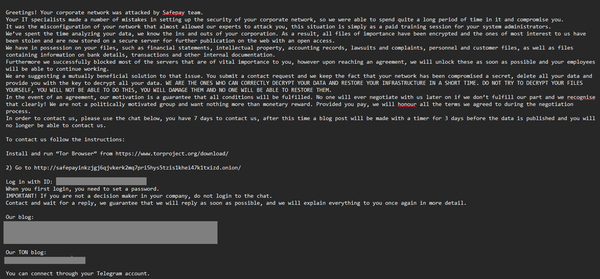
IT giant Ingram Micro's systems shut down after SafePay ransomware attack
Qantas is talking with threat actor after attack, Android spyware flaw exposes thousands of customers, Ransomware negotiator may have struck deals with hackers, US sanctions bulletproof hoster, US goes after DRPK "IT worker" program, A racist hacked Columbia and the NYT shamed itself, much more