UK spy chief warns of escalating Russian cyber aggression
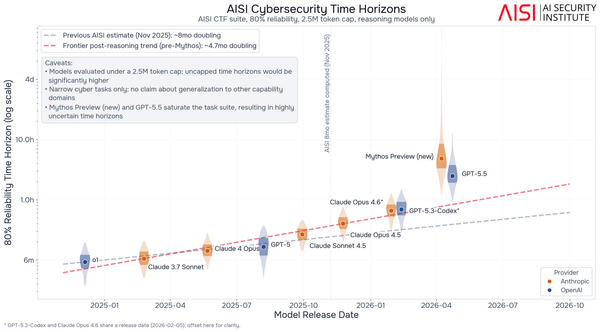
India's banking and government institutions are testing Mythos, Charter confirms breach claimed by ShinyHunters, Play ransomware gang hit Mike Lindell's MyPillow, Fake UK visa portal exposes passports and selfies, CrowdStrike shuttered C2 for Glassworm botnet, much more